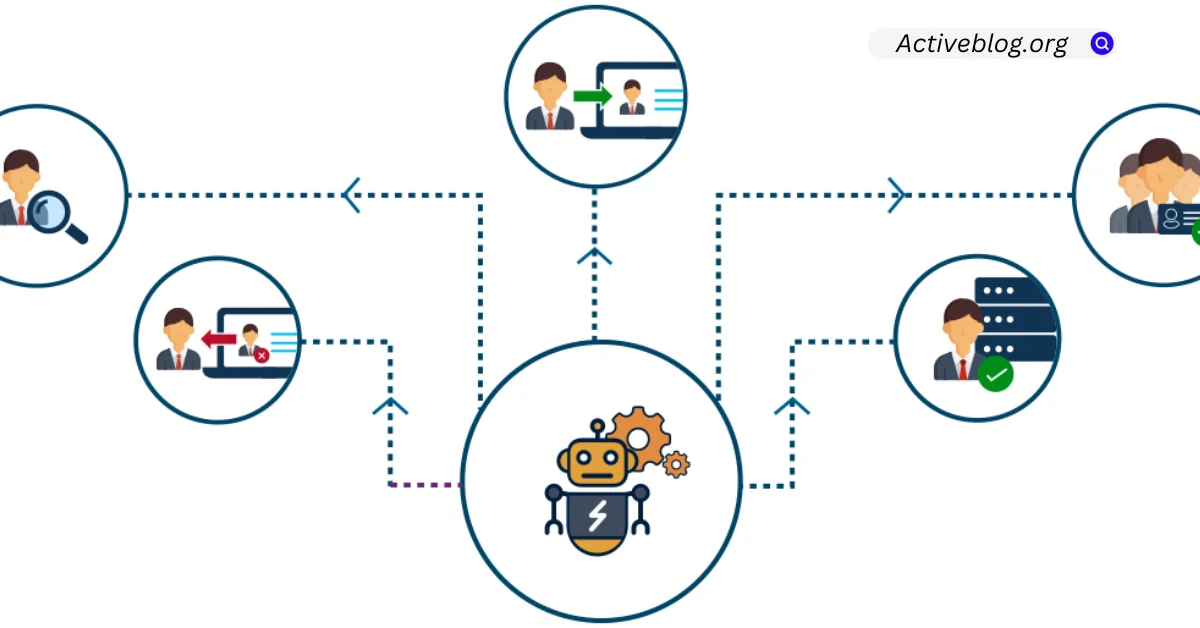
The identity lifecycle includes a significant and resource-intensive component called access request management. In accordance with national and international security and privacy laws, administrators provide and de-provision user access to data, apps, and devices.
Automating access requests eliminates manual burden, accelerates approval times, and makes it easier to ensure continuous proof of compliance. Learn more about why you should automate your access management processes.
Increased Compliance
In addition to automating repetitive tasks, a good IAM solution also allows for self-service capabilities, such as users requesting access or resetting their passwords, which reduces the burden on IT support. It also enables organizations to scale their IAM processes, reducing the risk of error and enabling them to manage access to increasingly expansive digital resources.
IT departments and business leaders can implement and enforce granular user access management and compliance with automation. This includes the ability to conduct frequent user access reviews, ensuring that access privileges are aligned with the principle of least privilege. It also ensures that all users have minimum permissions and that unnecessary or excessive privileges are removed.
Additionally, automation enables organizations to proactively identify and address security risks associated with inappropriate or unused access privileges. It can also help them achieve compliance with industry standards and regulations by implementing standard access policies based on job roles and responsibilities. This helps to ensure that users are only granted access to the assets they need and eliminates the need for ad-hoc exceptions.
Increased Efficiency
Companies may reduce manual data entry and help desk calls by automating their IAM operations. This increases overall productivity by enabling workers to concentrate on more crucial things.
For example, imagine that a new employee comes on board and needs access to 20 systems. With a manual process, this might take weeks to complete. This is a waste of time and a major inconvenience for the new employee who needs help getting their work done.
By automating the process, managers and system owners can automatically pull information about accounts and access rights from target systems into an IAM solution and update them accordingly. This allows quicker, more accurate access reviews, which is helpful in meeting compliance requirements.
In addition, automated IAM solutions can help to improve security by reducing the amount of unnecessary access. Using role-based and policy-based access, an IAM solution can evaluate user attributes such as job roles, organizational memberships, management level, and other factors to determine the appropriate level of access. This helps reduce the number of unneeded access privileges and ensures that users are only granted access based on their needs.
Reduced Risk
Access control management is a difficult undertaking that is readily compromised by human mistakes. This may lead to illegal access to private information and assets, or possibly a complete data breach. By offering a secure mechanism to control access quickly, automation helps to lower risk.
The danger of too-privileged access is decreased by the automated system, which establishes and modifies permissions depending on roles, responsibilities, and organizational structure. Additionally, it makes sure that access is only given to those who require it and that it is immediately revoked when a person quits a job.
By implementing tough authentication rules and stringent security guidelines, an efficient IAM system may also guarantee compliance with industry requirements and reduce the danger of cyberattacks and internal data breaches. This can assist businesses in avoiding exorbitant penalties and punishments. Businesses may relieve the burden on their IT team and boost employee productivity by automating this procedure.
Increased Security
As digital assets grow, tracking who has access to what becomes harder. While it’s important to authenticate the identity of someone attempting to access a resource, granting them the correct level of access to that resource is equally important.
This unified identity management platform eliminates the need for IT teams to adjust user accounts manually, reduces the risk of security breaches, and makes it easier to comply with industry regulations and standards. It also frees up valuable IT resources that can be reallocated to other critical projects. In the end, this helps drive efficiency and productivity within the business. Using a centralized system for managing user accounts and permissions enables users to log in once to gain access to all the systems they need for work.
Increased Productivity
Automating access management processes lowers the need for IT administrators to handle manual tasks and enables them to focus on more complex projects. This frees up vital resources that can be refocused toward business goals and increasing organizational productivity.
A good IAM solution will automatically provision a new employee’s account and associated security groups upon their hire date. This allows them to be productive when they start and reduces the risk of unauthorized users getting in. It will also ensure that the user has the right level of access based on their role.
The process must be easy for managers regarding periodic access reviews and certifications. A centralized portal to manage access requests and a simple and consistent approval process that ties back to the company’s access policies is crucial.
Another important feature is the ability to revoke access immediately when an employee leaves the company, ensuring the right access levels are always in place. This prevents the risk of data breaches and other security incidents that can be costly to a business.